If you searched for anon vault, you likely want to understand what it is, whether it protects privacy, and how it compares to other anonymity or secure-storage solutions. The same phrase can sometimes be used in different ways across forums, apps, and marketing pages, so it’s important to treat it like a starting point and confirm the exact product or service behind the name.
This article explains how to research anon vault like an SEO and due-diligence task. We’ll use an Ahrefs and SEMrush-style approach, looking at intent, related queries, SERP patterns, and topic clusters, to build a clearer picture of what anon vault does, how users describe it, and what safety checks you should run before trusting it with anything sensitive.
Legitimacy and privacy safety signals
When evaluating anon vault, focus on “trust evidence,” not only marketing claims. Privacy-focused tools should have concrete, verifiable details such as published documentation, clear threat models, understandable security practices, and transparent statements about encryption or key handling. If a site offers vague assurances like “we are private” without explaining mechanisms, that’s a warning sign.
Also pay attention to the user journey. Many privacy tools require setup steps such as accounts, browser configuration, extensions, or wallet-style keys. The more steps that involve permissions or sensitive data, the more you should require clarity about what’s collected, why it’s collected, and how it’s protected. Treat each step as an opportunity for either strong safeguards or hidden risk.
Feature checklist
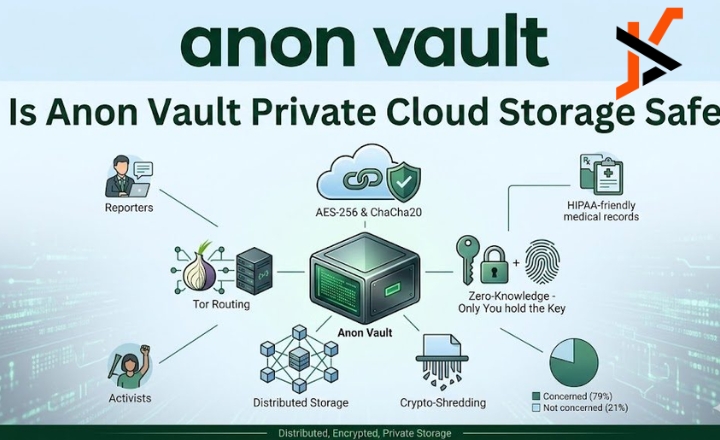
Start with core security expectations. For anon vault, you should look for plain-language explanations of encryption at rest and in transit, authentication method options (if any), and whether it supports end-to-end encryption or client-side encryption. Also, look for audit or assessment references, such as third-party reviews, bug bounty programs, or published security notes. A credible privacy tool usually explains what it does well and what its limits are.
Next, check transparency signals. A trustworthy service tends to have clear documentation, understandable FAQs, and consistent answers across pages. If anon vault has changing claims, missing policy pages, or unclear ownership, users often report confusion or lack of support. In an Ahrefs/SEMrush mindset, think of these as “content coverage gaps”: if the SERP indicates broad interest but the documentation is thin, your confidence should drop.
Privacy safety checklist (threat model and data handling)
A real privacy solution should have a stated threat model. For anon vault, ask what it protects you from: hackers, platform administrators, phishing, device compromise, metadata leakage, or government-level requests. Not all privacy systems protect against all threats, and unclear threat models can lead to false confidence. When reading descriptions, look for words like “metadata,” “logs,” “retention,” “collection,” and “anonymity guarantees,” then verify they’re explained nearly.
Also consider operational privacy. Many services unintentionally expose users through logs, telemetry, account identifiers, or recovery mechanisms. If anon vault includes backups, sharing links, or recovery workflows, examine whether those create new exposure routes. In SEO-style due diligence, you’d compare how top pages and user discussions talk about these points, consistency across multiple sources usually indicates fewer surprises.
Research using Ahrefs and SEMrush-style
SEO research methods are useful for security research because they reveal intent clusters and content alignment. For anon vault, related keywords can help you find the “right” information faster: not only what it is, but also whether users trust it and how it behaves in real scenarios. You aim to triangulate, official documentation, independent reviews, and user-reported experiences.
Use the phrase anon vault together with modifiers. Search variations like “anon vault reviews,” “anon vault legit,” “anon vault pricing,” “anon vault security,” “anon vault encryption,” “anon vault how to use,” and “anon vault support.” You can also use broader related keywords such as “anonymity,” “secure storage,” “encrypted vault,” “private browsing,” “threat model,” “zero-knowledge,” and “end-to-end encryption.” This creates a mini-topic cluster and makes it easier to separate informational content from promotional fluff.
Interpret intent clusters to find the right kind of evidence
Ahrefs and SEMrush approaches often classify queries by intent: informational (what is it), transactional (pricing/how to start), navigational (login or official site), and comparative (“best vault,” “alternatives”). With anon vault, you should prioritize sources that match the evidence type you need. For example, “security” and “encryption” intent should lead to technical pages or detailed explanations, not only generic descriptions.
Then filter for query “quality.” People searching “anon vault scam” may be responding to a bad experience, but the results might be biased or incomplete. Meanwhile, “encryption,” “audits,” “privacy policy,” and “terms” queries tend to yield more concrete documentation. The practical step is to read multiple result types and note whether they describe the same core behavior for anon vault.
Make a safe decision about using anon vault with staged testing and risk controls
Once you gather enough evidence, decide how to proceed. Even if anon vault looks credible, privacy tools can still differ in performance, usability, or data-handling details. The safest approach is staged testing: start with low-risk actions, then gradually increase your trust level as you confirm behavior.
This is especially important for anything that touches identity, payment, backups, or key recovery. If you are evaluating whether anon vault truly protects confidentiality, don’t begin by uploading sensitive files or entering personal data you can’t replace. Start with benign test data and observe how the tool stores it, whether you can access it later, and how it behaves during sharing or export.
Staged onboarding (start minimal, then increase)

Begin with a controlled setup. Create a test account or use a minimal profile if possible, and avoid reusing passwords from other services. For anon vault, confirm what permissions it requires: browser access, device storage, microphone/camera (if relevant), and notification permissions. If you see unnecessary permissions, reconsider whether you trust the application’s intent.
Next, test basic workflows with non-sensitive content. Try storing a small text note or dummy file, then validate whether access control works as described. Check whether the tool creates public links by default, whether there’s a “delete” option, and whether data is recoverable after deletion attempts. These are operational checks that help confirm anon vault matches its stated privacy promises.
Conclusion
The keyword anon vault can point to different services or concepts, so the most important step is validating what you’re actually using and whether its claims match evidence. By checking documentation, policy pages, security explanations, and user experiences, you can reduce the risk of trusting something that doesn’t deliver real privacy protections.
Then use Ahrefs and SEMrush-style research thinking to build a related-keyword cluster, interpret SERP intent patterns, and compare against alternatives. When anon vault aligns with consistent explanations across credible sources, and when your staged testing confirms expected behavior, you can make a safer decision about whether it’s the right privacy solution for your needs.

